-
Be sure to read this post! Beware of scammers. https://www.indianagunowners.com/threads/classifieds-new-online-payment-guidelines-rules-paypal-venmo-zelle-etc.511734/
You are using an out of date browser. It may not display this or other websites correctly.
You should upgrade or use an alternative browser.
You should upgrade or use an alternative browser.
Off to an Information Security conference
- Thread starter wtburnette
- Start date
The #1 community for Gun Owners in Indiana
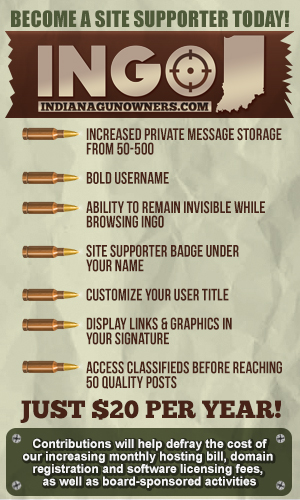
Member Benefits:
Fewer Ads! Discuss all aspects of firearm ownership Discuss anti-gun legislation Buy, sell, and trade in the classified section Chat with Local gun shops, ranges, trainers & other businesses Discover free outdoor shooting areas View up to date on firearm-related events Share photos & video with other members ...and so much more!
Member Benefits:
I guess that means no...lol.
no --- was any invited ?
That's what this thread was intended to find out. I was interested to see if any INGO members also worked in the Information Security field. I know there are a few who are in IT, just wasn't sure if there were any in InfoSec.
eldirector
Grandmaster
I'm guessing (actually, I really, really hope) that a few of my co-workers are attending.
Huge field right now, considering the wealth of information collected on nearly everyone, and the ****-poor security most is guarded with.
Looking forward to your AAR!
Huge field right now, considering the wealth of information collected on nearly everyone, and the ****-poor security most is guarded with.
Looking forward to your AAR!
I'm guessing (actually, I really, really hope) that a few of my co-workers are attending.
Huge field right now, considering the wealth of information collected on nearly everyone, and the ****-poor security most is guarded with.
Looking forward to your AAR!
The conference was fantastic, as it always is (this is my 3rd year attending). Networking with both industry peers and the major vendors in the field is very helpful and informative. There were two great speeches given, discussing where the industry was and listing things that companies should be looking into, plus there were some very good breakout sessions focused on specific areas, such as network architecture, social engineering, new products for discovering and tracking intrusions and infections and more. It was a long day, but it was a lot of fun and I learned a lot. Just sad I wasn't able to attend the small dinner one of the vendors was having over at the Colt's Grill afterwards.
eldirector
Grandmaster
So.. What are the hot topics? A short list of major security concerns for 2016? What tools/tech/policies should folks be looking at?
I want to sound smart in front of my IT and Development groups.
I want to sound smart in front of my IT and Development groups.

The big things weren't any technology, but architecting your network with security in mind (lots of segmentation for one thing), making sure you're following least privilege and least access principles and also that breaches are going to happen, but how quickly you can detect and stop is the main thing. One of the big technologies was SSL decryption. One blind spot is SSL encrypted traffic on your network that you don't know the content of. There are several products that decrypt it, allow you to analyze and then re-encrypt and send out to it's destination. Those are the biggest takeaways I had.
I am interested in Infosec, working on my CISSP and want to get into Information Security full time, right now I am the Director of Information Systems for a law firm so I have had to educate myself. Any tips for making the the change to going completely into security?
I am interested in Infosec, working on my CISSP and want to get into Information Security full time, right now I am the Director of Information Systems for a law firm so I have had to educate myself. Any tips for making the the change to going completely into security?
That's a tough question, mostly due to the level you're at already. If you can get the CISSP, that will definitely help. You can work with any number of placement firms, which could help you get on somewhere in the InfoSec field. The other thing I can recommend is to watch big InfoSec employers for openings: Anthem, Eli Lilly, Sally Mae, IU Health, etc. That's how I got into the field. My buddy worked for one of these employers and since I had 16 years in the Support side of the industry, he helped me find an entry level position helping to design the Desktop Vulnerability Management program.
Also, have you looked into the CompTIA Security+ certification? It can be a nice stepping stone cert. It's nowhere near as in depth as the CISSP, but covers most of the information, which is info on all of the security domains.
So, man in the middle?The big things weren't any technology, but architecting your network with security in mind (lots of segmentation for one thing), making sure you're following least privilege and least access principles and also that breaches are going to happen, but how quickly you can detect and stop is the main thing. One of the big technologies was SSL decryption. One blind spot is SSL encrypted traffic on your network that you don't know the content of. There are several products that decrypt it, allow you to analyze and then re-encrypt and send out to it's destination. Those are the biggest takeaways I had.
I thought SSL was meant to stop man in the middle attacks* using a CA.
* One man's "allow you to analyze" is another man's attack.
So, man in the middle?
I thought SSL was meant to stop man in the middle attacks* using a CA.
* One man's "allow you to analyze" is another man's attack.
That's my reaction too. But owners of businesses have the right to enforce their policies, which generally include the right to monitor what you are doing on their network and time. The good news is that is it fairly easy to figure out if they are doing this type of SSL breakage.
Least privilege? Isn't that a 40-year old concept now? Sad that it needs to be a major topic and not assumed and mentioned in passing.
That's my reaction too. But owners of businesses have the right to enforce their policies, which generally include the right to monitor what you are doing on their network and time. The good news is that is it fairly easy to figure out if they are doing this type of SSL breakage.
Least privilege? Isn't that a 40-year old concept now? Sad that it needs to be a major topic and not assumed and mentioned in passing.
Well, the biggest thing with least privilege is how often it's not used, just like proper network segmentation and other such standard, well known concepts. Take the Target breach for example. Malicious actors got in by compromising the network of an HVAC contracting company. Instead of giving that company only rights to remotely access the HVAC system, they also had access to the POS system. The POS system, once accessed, had access to other parts of the network that also didn't make sense. Bottom line was that there were multiple failures of standards in play and any one of them could have prevented, or greatly lessened the impact of, the breach. Too many companies, in my experience, accept risk they shouldn't accept, usually in the name of convenience, then turn around and blame their InfoSec team when they get bit in the ass by poor decision making. Normally, there is plenty of blame to go around. Execs, infrastructure management, etc.
That's my reaction too. But owners of businesses have the right to enforce their policies, which generally include the right to monitor what you are doing on their network and time. The good news is that is it fairly easy to figure out if they are doing this type of SSL breakage.
I believe the reaction was the same as mine, not whether a company was allowed to do it but I was under the impression SSL was not able to be decrypted by anyone but the receiver.
I believe the reaction was the same as mine, not whether a company was allowed to do it but I was under the impression SSL was not able to be decrypted by anyone but the receiver.
I had the same confusion. No one really explained it in depth, so I'm not sure exactly how it was being done.
Decrypting is really, really hard.I believe the reaction was the same as mine, not whether a company was allowed to do it but I was under the impression SSL was not able to be decrypted by anyone but the receiver.
My guess is they get you to connect to the man in the middle by pretending to be Amazon, then that middle man connects securely to Amazon and pretends to be you; so there's two SSL connections. But your computer should say, "The computer you're connecting to use using Amazon's certificate, but it's not an Amazon server. This is really sketchy and I don't want you to do this."
You <----- SSL -----> middle man <----- SSL -----> Amazon
This is why there's a Certificate Authority - someone that will vouch for Amazon's server. The mathematics of cryptography is pretty easy (relatively speaking), it's the issues with trust that are harder to deal with. I.e. how can you trust that this computer that you're about to establish an encrypted communication line is really who they say they are?
Decrypting is really, really hard.
My guess is they get you to connect to the man in the middle by pretending to be Amazon, then that middle man connects securely to Amazon and pretends to be you; so there's two SSL connections. But your computer should say, "The computer you're connecting to use using Amazon's certificate, but it's not an Amazon server. This is really sketchy and I don't want you to do this."
You <----- SSL -----> middle man <----- SSL -----> Amazon
This is why there's a Certificate Authority - someone that will vouch for Amazon's server. The mathematics of cryptography is pretty easy (relatively speaking), it's the issues with trust that are harder to deal with. I.e. how can you trust that this computer that you're about to establish an encrypted communication line is really who they say they are?
I doubt a company would use that as a security method, seems like it would open them up to more risks than anything else.
Fairly simple. The procedure listed below is implemented via an SSL proxy. JettaKnight gives a good visual representation.
1) The company adds their own CA cert on your device so that it accepts any SSL certs created by the company as valid (that is, no pop-ups for certs created and served by the company).
2) Any https: request made on the company network passes through the network SSL proxy. That proxy generates a certificate for the destination signed by the company CA (ex: https://www.google.com signed by acme.com CA). Your browser accepts the connection because it trusts the company CA is providing a valid certificate for Google.
3) The proxy logs the request and then forwards the request via https: to google.com and accepts the proper google.com certificate to encrypt that second connection.
4) The proxy gets the data back, decrypts using the proper cert and logs any info.
5) The proxy encrypts the return info using the company-generated google cert and returns that info to the browser.
99.9% of people on corporate networks will continue browsing and never notice the difference. However, if you are suspicious, determining if the company is using an SSL proxy is trivial. When you go to an SSL web site, click on the lock and examine the certificate details. If it is a valid certificate, it will be signed by Verisign, Thawte or other valid CA. If it is an SSL Proxy, the cert will be signed by the company's domain.
1) The company adds their own CA cert on your device so that it accepts any SSL certs created by the company as valid (that is, no pop-ups for certs created and served by the company).
2) Any https: request made on the company network passes through the network SSL proxy. That proxy generates a certificate for the destination signed by the company CA (ex: https://www.google.com signed by acme.com CA). Your browser accepts the connection because it trusts the company CA is providing a valid certificate for Google.
3) The proxy logs the request and then forwards the request via https: to google.com and accepts the proper google.com certificate to encrypt that second connection.
4) The proxy gets the data back, decrypts using the proper cert and logs any info.
5) The proxy encrypts the return info using the company-generated google cert and returns that info to the browser.
99.9% of people on corporate networks will continue browsing and never notice the difference. However, if you are suspicious, determining if the company is using an SSL proxy is trivial. When you go to an SSL web site, click on the lock and examine the certificate details. If it is a valid certificate, it will be signed by Verisign, Thawte or other valid CA. If it is an SSL Proxy, the cert will be signed by the company's domain.
Last edited:
eldirector
Grandmaster
I read this as the company owned the cert., and was using it to decrypt the traffic on its own network, before allowing it to leave the network encrypted. For example, if you are worried about corporate espionage, you could view the contents of encrypted communication on your own network. Without something like this, you could give a contractor a cert, and they could send any info using it, and you would only see "2 TB of encrypted traffic", and have no idea if it is the source code to your latest product, or cat pictures. With this, you can validate they are indeed cat pics, re-encrypt, and let them go to their destination.One blind spot is SSL encrypted traffic on your network that you don't know the content of. There are several products that decrypt it, allow you to analyze and then re-encrypt and send out to it's destination.
Members online
- possum_128
- DoggyDaddy
- 63PGP
- BP84
- TheSpookyCat
- jspy5
- Peacekeeper3073
- mkgr22
- Firehawk
- Jrich1852
- draftyranger
- Joniki
- Mgderf
- BackFromDC
- KittySlayer
- Nazgul
- Bassat
- NHT3
- gassprint1
- Vimace
- Floivanus
- fireball168
- Dean C.
- hhi7410
- BR8818
- morve80
- Huzrjim
- Tradesylver
- Altrex
- ComeJesuscome
- Dewidmt
- Kinkopet33
- johnx2
- actaeon277
- whatwehavehere
- Bethridge345
- XDdreams
- billyramair
- Demoderb1989
- BigMoose
Total: 6,099 (members: 46, guests: 6,053)